In the vast landscape of file-sharing services and downloadable utilities, new names frequently appear and generate curiosity. One such name that has been circulating online is 8tshare6a software. Promoted across forums, third-party download sites, and occasional pop-up ads, it claims to offer powerful file-sharing capabilities, optimized downloads, or system-enhancing features. But what exactly is it? And more importantly, should anyone actually download it?
TLDR: 8tshare6a software appears to be promoted as a file-sharing or download-enhancement tool, but its origins and legitimacy are unclear. Many versions are distributed through unofficial sources, which increases security risks. Users should approach with caution, verify sources, and prioritize cybersecurity. Downloading unknown software without proper research can expose systems to malware, data theft, or performance issues.
What Is 8tshare6a Software?
At its core, 8tshare6a is described in most listings as a file-sharing or download utility. Some websites portray it as a peer-to-peer transfer tool, while others claim it optimizes large file transfers across networks. However, there is no widely recognized developer or official website consistently linked to the software.
This lack of transparency raises early red flags. Legitimate software products typically have:
- An official website with documentation and support pages
- Clear company or developer information
- Version history and changelogs
- Verified downloads via trusted platforms
In contrast, downloads labeled “8tshare6a software” are often hosted on aggregator or third-party download platforms, commonly bundled with other offers or add-ons.
What Does 8tshare6a Claim to Do?
The functionality attributed to 8tshare6a varies depending on where it is listed. Some of the common claims include:
- Faster peer-to-peer (P2P) file transfers
- Compressed large file sharing
- Secure encrypted data transfers
- Bandwidth optimization
- Download acceleration features
These are attractive features for users who frequently transfer large files, share digital media, or collaborate remotely. However, the marketing descriptions often lack technical specifications or detailed explanations about how these improvements are achieved.
In cybersecurity circles, vague feature descriptions combined with frequent ad-based distribution can indicate one of several possibilities:
- The software is outdated and rebranded.
- The program may include bundled adware.
- It could function as a potentially unwanted program (PUP).
- In worse cases, it may contain hidden malicious components.
Where Is 8tshare6a Typically Found?
Users rarely encounter 8tshare6a through trusted digital marketplaces. Instead, it often appears in:
- Pop-up download advertisements
- Redirect pages during unrelated software installations
- Freeware bundle offers
- Torrent description pages
This distribution pattern is important. Legitimate software companies generally avoid aggressive redirection tactics or unsolicited download prompts.
Potential Risks of Downloading 8tshare6a
Downloading unknown utilities always carries certain risks. In the case of 8tshare6a, the absence of transparent ownership increases uncertainty. Below are the most common risks associated with similar software:
1. Malware Infection
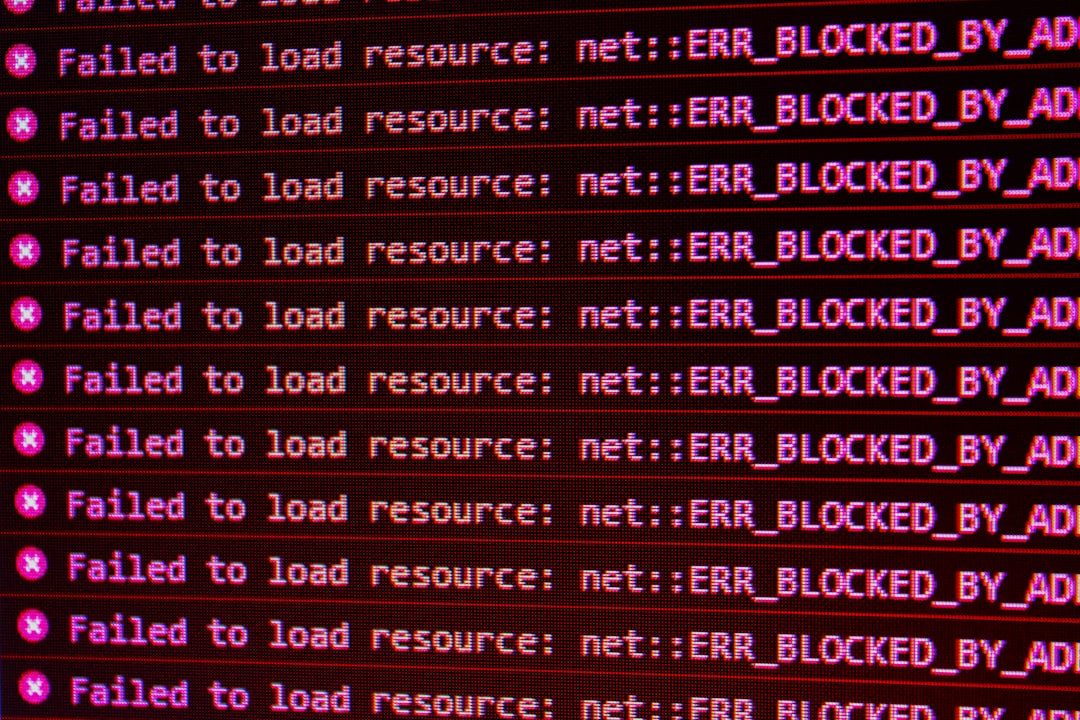
Unverified downloads can contain spyware, trojans, or ransomware. Even if the main application appears functional, hidden background processes could compromise system security.
2. Adware and Browser Hijacking
Some free download utilities inject ads into browsers or modify search engines. Users then experience:
- Increased pop-ups
- Redirected search results
- Homepage changes
3. Data Privacy Concerns
If the software connects to unknown servers, transmitted files and user data could potentially be intercepted or logged.
4. System Performance Issues
Programs that run continuously in the background may consume CPU, RAM, or network bandwidth, slowing overall device performance.
How to Evaluate Software Like 8tshare6a Before Downloading
Anyone considering downloading unknown software should follow a structured evaluation process:
- Search for independent reviews on cybersecurity websites.
- Check domain registration age for the official site (if one exists).
- Scan the file with antivirus tools before opening it.
- Verify digital signatures from recognized developers.
- Read user feedback carefully for consistent complaints.
If very little verified information exists, that is often a reason to avoid installation entirely.
Comparison: 8tshare6a vs. Recognized File-Sharing Solutions
To better understand where 8tshare6a stands, it helps to compare it with established tools in the same category.
| Feature | 8tshare6a | Recognized Cloud Service | Verified P2P Client |
|---|---|---|---|
| Official Website | Unclear or inconsistent | Yes | Yes |
| Developer Transparency | Limited | Full company info | Open source or registered company |
| Security Documentation | Not clearly available | Published policies | Public documentation |
| User Reviews | Sparse or mixed | Extensive and verifiable | Extensive community feedback |
| Distribution Method | Third-party sites | Official platforms | Official repositories |
The differences highlight why many cybersecurity experts recommend sticking with well-established alternatives.

Signs That a Download May Not Be Legitimate
Consumers should be alert for warning signals before clicking “Download.” These include:
- Urgency messages claiming the system is outdated
- Fake system scan results
- Unsolicited installer downloads
- No privacy policy or terms of service
- Requests for excessive permissions
Even if 8tshare6a seems to install properly, post-installation monitoring is critical. Unexpected network activity, new toolbars, or unknown scheduled tasks may indicate problems.
What To Do If You Already Downloaded It
If the software is already installed, recommended steps include:
- Run a full system antivirus scan.
- Check installed programs for unfamiliar additions.
- Review browser extensions and remove suspicious entries.
- Monitor system performance for unusual behavior.
- Consider reinstalling the operating system if serious compromise is detected.
Taking proactive action quickly reduces the potential impact of malicious components.
Why Software Transparency Matters
Modern software operates in a highly connected ecosystem. Applications often request:
- Network access
- File system permissions
- Administrative privileges
Without knowing who developed the software or where it sends data, users expose themselves to significant security risks. Transparent development practices, open documentation, and verified distribution are no longer optional luxuries—they are essential standards.
Final Thoughts
8tshare6a software appears to fall into a category of utilities that promise helpful features but lack publicly verifiable credibility. While it may or may not perform its advertised tasks, the uncertainty alone makes it risky. In cybersecurity, caution usually proves less costly than recovery.
Before installing any unfamiliar program, users should ask a simple question: Is the benefit worth the potential compromise? With limited information available about 8tshare6a’s developer, security standards, and distribution practices, many experts would recommend choosing established alternatives instead.
FAQ
1. Is 8tshare6a software legitimate?
There is no widely verified evidence confirming it as a well-established or officially recognized software product. Users should exercise caution due to limited transparency.
2. What does 8tshare6a claim to do?
It is typically promoted as a file-sharing or download acceleration tool, sometimes claiming secure and optimized transfers.
3. Is 8tshare6a safe to download?
Safety cannot be guaranteed, especially when downloads are hosted on third-party or ad-driven sites. Scanning files and verifying sources is strongly recommended.
4. Can 8tshare6a contain malware?
Any unofficial or unverified download has the potential to contain malware, adware, or other potentially unwanted components.
5. How can users remove 8tshare6a if installed?
Users should uninstall the program via system settings, run a comprehensive antivirus scan, and review browser extensions and startup programs.
6. Are there safer alternatives?
Yes. Well-known cloud storage providers and established peer-to-peer applications with verified developers and transparent security practices are safer options.
7. Why is there so little information about it?
Some software tools circulate through online promotion networks without a strong developer presence. Limited public records and unclear ownership make verification difficult.